Security must be at the core of your mobility strategy to protect corporate data, maintain compliance and ensure security across devices.

Password Management
Device passwords are the first line of defense against unauthorized access and ensure the protection of files and other data. Secure your entire business mobile fleet and easily set up password policies in accordance with your organization’s requirements with TinyMDM. Force users to choose a complex password and change it regularly, improving the security of your fleet.
Remote lock / unlock
Instantly lock mobile device to protect your data in the event of theft or compromised device. This option will secure the terminal by forcing the user to enter the password to unlock it. You can also remove the password and remotely unlock the device so the end user can regain access to it if needed.

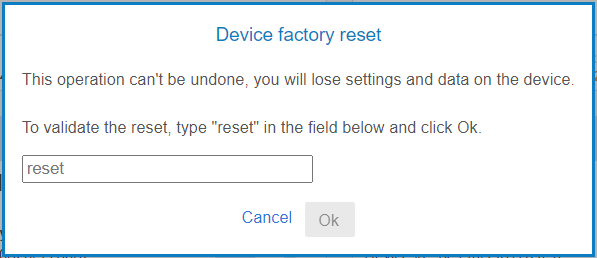
Remote Wipe
Don’t put your confidential data at risk and choose to remotely wipe out the device if lost or stolen. In full management mode this feature will reset the device to factory settings. You can also define a maximum number of erroneous password entries before resetting the device, in accordance with ANSSI recommandations (National Cybersecurity Agency of France). In work profile mode, it will delete only the business data from the device.
Block Factory Reset
Secure your entire business mobile fleet by preventing any Factory Reset attempt from end-users: when enabled, this setting won’t be accessible and an admin code will be needed to reset the device.


FRP Management
With our Android devices management software, you can securely manage FRP on all devices from your admin dashboard: either disable it so that the Google account verification step can be skipped in case of a factory reset, or enable it and add a Google account for FRP to be taken into account on all devices. What’s FRP?
Compliance Management
Track the compliance of your devices against your defined policies in real time: if a device is not fully compliant with your organizational requirements, take immediate action to remedy it.

